Security and Compliance at SecurityBridge
Trust is everything to us, but you can’t have trust without security. That’s why we use independent experts to verify our security, privacy, and compliance controls.

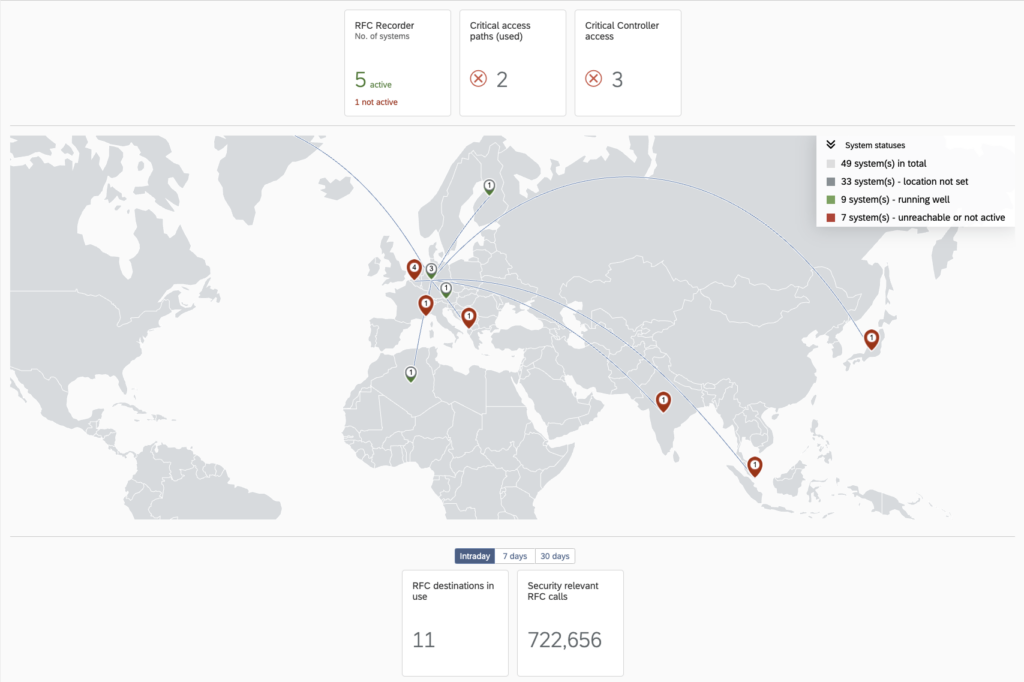
Protecting 8,000+ SAP production systems globally
“SecurityBridge helped us automate our SAP application monitoring and vulnerability by easily integrating with our SIEM platform. By doing this, we boosted security, lowered costs, and allowed our security team to focus on remediation,”
Thierry Eyraud, Digital Risk Leader
"With my extensive experience in SAP, it's clear that SecurityBridge fills the critical security voids that SAP can't address alone."
Jaromir Wróblewski, Group IT Infrastructure Manager
“We selected SecurityBridge as the platform with the largest functional scope and seamless integration within the SAP technology stack.”
Stéphane Peteytas, Head of SAP Cybersecurity
"With our SAP partner, myBrand Conclusion, and the SecurityBridge Platform, we can structurally manage our risks and improve our SAP Security."
Marianna Pothof van Bekkum, Functional Application Manager
"The SecurityBridge Platform is easy to use, and the great support helps us to run our SAP Security services efficiently, from the audit to remediation and patching all the way down to Threat Detection.”
Mauro Del Quondam, Information Technology
"With SecurityBridge, we can efficiently enforce secure configurations across our large SAP landscape. The Security Roadmap gives our small but specialized team guidance and helps responding to critical SAP vulnerabilities.”
Daryl Mennen, SAP Security Architect
"SecurityBridge has streamlined our security processes, allowing us to move beyond the traditional ways of working in SAP Security. It provides all the necessary tools, enabling continuous and efficient improvement of our SAP security posture "
Jean-Luc Turin, Identity and Access Governance Director
“The SecurityBridge roadmap was crucial in helping us prioritize SAP system hardening tasks. We were
able to more than double our security level in a very short time and reduce patching efforts.”
Jonas Grein, CIM System
“Our multi-channel concept places high demands on the availability and security of our SAP system. With
SecurityBridge, we were able to significantly reduce our efforts in this regard.”
Daniel Schlund, Head of IT
"We have gained the needed visibility to identify business relevant cybersecurity threats, harden the SAP
landscape and respond immediately to zero-day and other critical SAP cybersecurity events.”
Dragomir Vatkov, Director Cyber Security Architecture
"After the RFP, we scored each vendor. When we finished with the process, UCB Biopharma found that it was a unanimous score from everyone towards SecurityBridge in most of these areas"
Abhijeet Pathania, Global ERP Access Management and GRC Lead, UCB Biopharma.
“With SecurityBridge, you have many topics predefined, so you get the benefits directly. You have best practices from the market built in and don’t have to configure everything by yourself or rely on experts who know the tool. If you know the SAP ecosystem and the ERP world, you can get started quickly and get a fast overview through the dashboard.”
Dennis Kaps, Executive security expert, Deutsche Telekom
Inhouse SAP Expertise
SecurityBridge is built and run by SAP experts. We have some of the world’s most renowned SAP security talent in-house, working every day to secure our customers’ SAP systems. As the industry’s subject matter experts, we ensure that our platform delivers maximum value for our customers and truly understands the ins and outs of working with and within SAP.
SAP Certified to ensure protection and reliability
SAP Certification proves that our technology integrates smoothly with SAP solutions, giving customers confidence in their investment decisions. Before receiving SAP-certified status, certified solution providers must pass stringent qualification procedures based on SAP-endorsed integration technologies.
SecurityBridge regularly recertifies our products (at minimum once per year, based on the available SAP certification programs) to ensure they are formally compatible with all new SAP products and versions.
We are pleased to hold the following SAP Certifications:
- SAP S/4HANA Cloud, Private Edition
- SAP S/4HANA Cloud, Extended Edition



Your Security is Our Top Priority
Our vision is to bolster SAP systems to fight tomorrow’s cyber threats. As such, we are dedicated to building our products in a secure environment while deploying products that improve your systems’ reliability, security, and privacy. If you ever have questions about SecurityBridge security measures, please contact us.
Responsible Disclosure Policy
Updated and Effective: July 2024
As a leading solution provider of a cybersecurity platform for SAP customers, protecting our customers and partners is our highest goal. We use modern tools and processes to test our solutions for defects in the best possible way. Defined quality gates have been established to ensure that program errors that could lead to a vulnerability are detected early in development. Likewise, we undergo a separate testing protocol for each package leaving our premises, highlighting security aspects.
Data security is a top priority for SecurityBridge, and we believe that working with skilled security researchers can identify weaknesses in any technology.
If you believe you’ve found a security vulnerability, please notify us; we will work with you to resolve the issue promptly.
Disclosure Policy:
If you believe you’ve discovered a potential vulnerability, please email us at [email protected]. We will acknowledge your email within 24 hours.
Please give us reasonable time to resolve the issue before disclosing it to the public or a third party. We aim to resolve critical issues within 24 hours of disclosure.
Make a good faith effort to avoid violating privacy, destroying data, or interrupting or degrading the Issuer Direct service. Please only interact with accounts you own or have explicit permission from the account holder.
Research Policy:
While researching, please refrain from:
Distributed Denial of Service (DDoS)
Spamming
Social engineering or phishing of Issuer Direct employees or contractors
Any attacks against SecurityBridge’s physical property or data centers.
Thank you for helping to keep SecurityBridge Direct and our Customers safe!