Prerequisites for an AI-driven SAP Security – Part 1: Patching

Chapters
Share Article
In our last article, we talked about the potential of AI to improve your SAP Security posture. An AI-driven Threat Detection approach can help identify sophisticated cyberattacks, especially those leveraging a chain of vulnerability exploits. However, while AI can point you to those issues and may automatically block certain activities or user endpoints, the SAP Security team remains responsible for responding to the attack.
Reducing attack surface is key
Ideally, the SAP Security team is ahead of the potential threat by continuously hardening the SAP system. Therefore, reducing the attack surface of an SAP system through hardening is a prerequisite for any AI-driven SAP Security approach.
The attack surface is the sum of all possible entry points or attack vectors, where an unauthorized attacker can access a system or application to extract data or manipulate sensitive information. The smaller the attack surface, the easier it is to protect. The SAP attack surface is by nature quite large, and reducing it means implementing various best practices, as mentioned in this article.
Patching helps reduce the attack surface
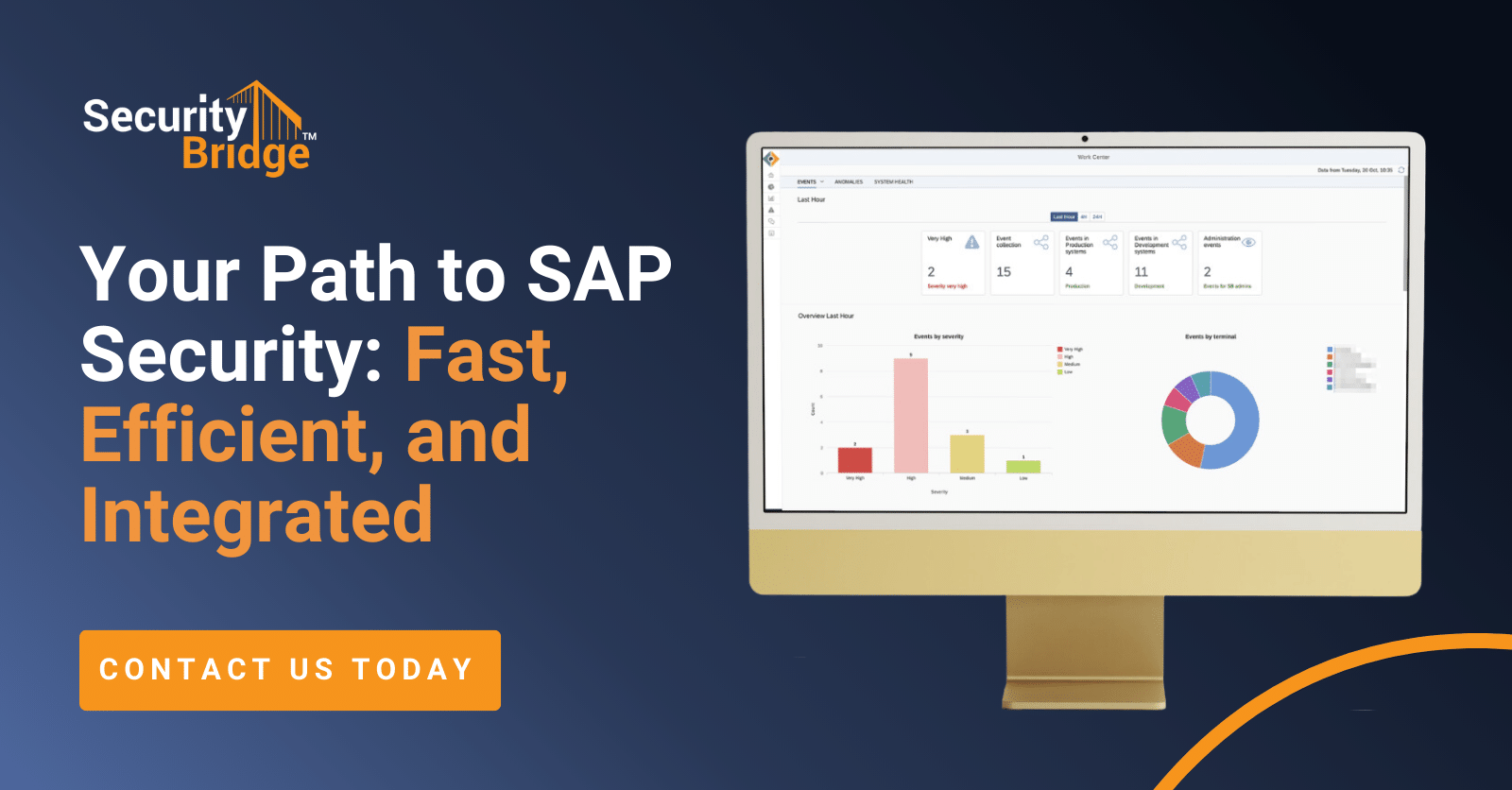
Among those best practices for hardening the system and reducing its attack surface, the mitigation of known vulnerabilities is one of the most straightforward tasks to start with. Every month, SAP releases patches for known vulnerabilities in SAP systems. Understanding their severity, their impact on your SAP landscape and their relevance to a specific system is key for efficient and short-term system patching. Therefore, SecurityBridge helps customers with a guided approach to balance between patch severity and implementation effort within the relevant patches for a specific SAP system. This allows customers to burn down their SAP patch implementation backlog efficiently and fast.
Automation and live recommendations allow efficient patching
Automating the implementation of SAP notes and patches is an additional way to increase the efficiency of this process in the customer’s organization. While this is obvious from a high-level perspective, SAP Security experts know how complex and heterogeneous the SAP patch management topic is. This makes automation very challenging. Nevertheless, SecurityBridge is also innovating in this area of SAP Security by providing automated implementation for the majority of SAP Notes. Only patches without manual steps and are considered safe to be deployed in the target system are released through this automated procedure. SecurityBridge performs a special internal patch assessment to ensure safety in this case.
Following the principle of a guided approach, SecurityBridge helps customers with recommendations for each vulnerability finding and SAP patch, based on expert knowledge and feedback from our community. Every newly discovered vulnerability starts a race between attackers and defenders, who can only win by either implementing compensating controls or if available, installing the patch before the exploitation. As time is of the essence in this scenario, SecurityBridge provides live recommendation updates to all customers, so they can instantly benefit from the community feedback.
Interested to learn how we can help you adopt a mature SAP Patch Management and other best practices for further hardening your SAP landscape? Contact us and we will be happy to tell you more about our guided approach to SAP Security excellence. For more SAP security-related news, articles, and whitepapers, please follow us on LinkedIn!