Story of a CISO – My Journey into SAP Cybersecurity

Chapters
Share Article
Key Takeaways
- Although storing the “crown jewels” most SAP systems are still not properly secured
- Securing SAP is a big challenge – even for an experienced CISO
- Bridging the gap between SAP engineers and the cybersecurity team is crucial
Getting started
When I initially started my journey into SAP cybersecurity, I already had many years of experience leading information security across various government organizations and large, multinational companies. Throughout this time, I met with many different CISOs and I started noticing a trend where SAP platforms were not protected to the level of other enterprise systems. In general, there was no focus on SAP security. Although for all those companies, SAP was one of the top few critical applications supporting some of the most critical business processes and holding some of the most sensitive data. So, I was wondering why is that the case? Why are so many companies neglecting something so important? I first decided to get my team to onboard SAP log sources to our SIEM and build correlation use cases so we could at least effectively monitor the “crown jewels” with our Security Operations Center (SOC).
SAP security requires deep application knowledge
After developing only a few basic use cases, we decided that the deep application knowledge required, and the lack of context in individual SAP log sources, made this effort much more complex than initially envisioned. And that project would have only covered the monitoring part! That’s when I went out looking for a commercial solution to close the SAP security gap at my company. I wanted a solution that would seamlessly integrate SAP landscape visibility into my existing security technology stack, and program, in a way that took the burden of deep SAP knowledge off the cybersecurity team.
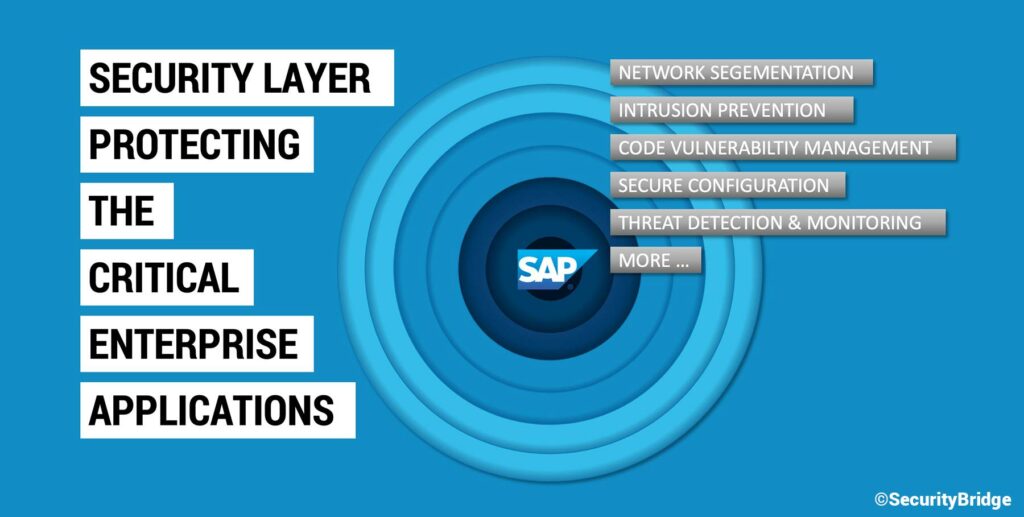
A lot of information security experts I talk too, that have not fully explored SAP, assume it’s just a standard application with a database. But there is a complex architecture, and more than a dozen log sources behind the scenes that need to be fully understood in order to apply adequate security controls. Then, you have the concept of clients to separate the individual business areas from each other and a unique way of interfacing to exchange sensitive data. Overall, SAP is a technical landscape like no other in the enterprise, that requires deep expertise to properly secure. Moreover, there is a distinct language barrier between SAP engineers and cybersecurity engineers where it is often difficult to even describe security controls in the same way as you would for the more traditional IT environment.
Software must be more than just a technical bridge
When I started to implement solutions for SAP cybersecurity using only my internal team, I was going purely after threat detection. However, after getting more experience with SAP, I realized that there were many other areas I needed to address such as preventative controls and compliance requirements.
This was simply more than the security team could keep up-to-date and implement on their own. Also, the integration of just SAP security audit logs to the SIEM did not even solve the monitoring part of the problem. They just do not provide enough information to detect or action on incidents, and there are too many logs left that you would need to correlate to build use-cases. I would say any security team that has tried to work with log management understands that it’s a very high volume and high friction situation to store all logs while typically only a small subset of that is relevant to SAP security. During that phase I spoke to the SAP teams and learned that most of SAP’s logs are filled with verbose business transactional information. We realized that those business transaction logs were often of low-security value, but at the same time provided some very important insights that were needed to fully understand entries in the primary security log: SAP Security Audit Log.
What we needed was a solution that helps us highlight findings and alerts with context, enrichment and normalization to get valuable information. A big part of cyber defense is the finding the so-called needle in the haystack and obviously the bigger the haystack, the harder it is to find the needle. So, any time we have a technology that’s able to really zoom-in into the focus area we need to investigate an incident, the better.
Finally, I came across the SecurityBridge platform and it provided all the primary security controls we were looking for, including incident detection, patch management, code analysis, and things that we could use for compliance and internal audit as well.