Your BW/4HANA System: Is it truly Cyber-Resilient?

Chapters
Share Article
A lot of SAP customers and consultants look at SAP BW/4HANA as a “lower-class” SAP system. Something for “someone else” to worry about. They forget about all the work that went into setting up their company’s Data Warehouse in SAP BW/4HANA… or further back, like some of my early SAP Consulting projects… on BW7 and BW3.5. And now, with the big push for S/4HANA migrations by 2027, the priority for anything related to BW seems to be going lower and lower. It sounds like the perfect place to attempt an exploit… in a forgotten system. This post can serve as your reminder to protect your investment in SAP BW/4HANA.
And if you are still running on BW7, you can listen in. Most of this will still apply to you, as well 😉
Why Protect BW/4HANA?
💡 It contains your company’s most important Data.
Think about “Big Picture” Data Flow: The most important system to protect is your S/4HANA since it is the as “system of record” for so much data. Also, remember that BW/4HANA is a key “downstream” system which contains much of the same data. The Business Warehouse (BW) architecture is set up by design to extract important data from S/4HANA, stage it, and make it readily available in BW/4HANA. It is a Data Warehousing Architecture, after all. So, the data protection policies and investments in place for the data in S/4HANA should carry over and be in place to protect the data on BW/4HANA as well.
Think Logically – You have invested so much to protect your ECC and S/4HANA primary systems. Then, you set up approved Data Extractors to copy much of your most valuable IT assets (DATA) onto this BW system. . . But then you fail to protect that same valuable Data on the BW system?? That doesn’t make sense. Right?
Think about Public Impact – Risk of Damage to Reputation: If your company’s BW/4HANA system is breached, the public will not care whether the sensitive data was obtained from an S/4HANA system versus a BW/4HANA system. The public PERCEPTION will simply be that your company has a “data problem” and trust in your company’s brand will go down. In a more extreme case, a business partner (customer, vendor, employee, or former employee) could pursue legal action if they can show harm from your company’s data breach.
Why Protect BW/4HANA?
💡 It’s going to be around for many more years.
Recently, I have interacted with over a hundred BW/4HANA consultants. From those discussions, I have 3 top observations:
There is some early movement to migrate (or at least, integrate) to SAP Datasphere.
Most customers are staying on BW/4HANA for the near future.
Consultant interest in learning BW/4HANA and getting certified is still VERY high. Meanwhile, I am not seeing as much demand to learn and get certified on SAP Datasphere.
S/4HANA is the main reason for this delay in moving from BW/4HANA to SAP Datasphere. S/4HANA is taking more time, budget, & resources than previously anticipated. The hyperfocus on S/4HANA will naturally occur during the ECC to S/4HANA initial migration. S/4HANA will also compete for focus in follow-on projects around optimizations and integrations.
Meanwhile, SAP has released two “Statements of Direction” for BW and SAP Analytics. These documents help SAP BW Customers with Roadmap Planning:
The BW Statement of Direction
BW covers: BW, BW/4HANA, and SAP Datasphere
SAP confirms support for BW/4HANA until 2040!!
The SAP Analytics Statement of Direction
SAP Analytics covers: Business Objects, Crystal Reports, Lumira, and SAP Analytics Cloud.
SAP Analytics Products are separated from BW, but certainly, the two groups of products are deeply connected. So, they should be considered together in the overall migration planning process.
(BIG BANG migrations excluded) If companies are already feeling the pressure to move from ECC and migrate to S/4HANA by 2027. . .and if BW/4HANA is supported until 2040. . .then in most cases, SAP BW customers will defer any migration from BW/4HANA to SAP Datasphere until AFTER they are stabilized on S/4HANA.
Since BW/4HANA is going to be around for a while, you need to include it in your scope for SAP CyberSecurity.
What is the top Cyber Risk for BW/4HANA?
💡 Data Exfiltration
Think like a Hacker – if you wanted to exfiltrate data from a company. And you knew they had the same data on 2 different servers… Thinking like a hacker, you would go after the data on the more vulnerable server.
…But it gets worse… the more vulnerable server is also less likely to detect the exfiltration activity! This type of exploit is known as “Silent Exfiltration” … your company could lose data… without even realizing it!!! The attack would never be detected… until your company’s proprietary data was discovered accidentally “in the wild” … outside of your company. And then, MAYBE it could be traced back to a breach period on the BW system.
Think Data Sensitivity – Where does your BW/4HANA system get its data? S/4HANA is the major data source for BW/4HANA. The data that comes over from S/4HANA to BW/4HANA has the same sensitivity and should have the same or similar protection as it had in S/4HANA.
How to protect BW ?
💡 Check the core: SAP Components - Basis
Many of the potential exploits that are possible on other SAP NetWeaver ABAP systems are possible also for BW/4HANA, even though it is no longer considered part of the SAP NetWeaver family of products. For example, SAP Patch Tuesday is still relevant for BW/4HANA system administrators in the same way that it is still relevant for S/4HANA system administrators.
I recommend the scanning and monitoring solution from SecurityBridge for BW/4HANA. SecurityBridge can perform well over a hundred specific compliance checks and it can monitor for potential exploit actions on systems that are built on the SAP ABAP stack… and, that still includes BW/4HANA.
How can I protect BW ?
💡 Tailor SAP CyberSecurity specifically for BW-related vulnerabilities
SecurityBridge can help you make your BW/4HANA system more Cyber-Resilient. Your BW system has some unique qualities that distinguish it from other SAP systems. Did you know:
There are SAP Security Notes that are specific to BW components.
There are SAP Authorization Objects that only exist in BW.
There are SAP Transaction Codes (aka T-codes) that only exist in BW.
✔️ Check for Missing SAP Security Notes that are specific to BW/4HANA
Utilize the SecurityBridge Patch Management capabilities on BW/4HANA to make sure that all the SAP Security Notes that are specific to BW components are checked and confirmed to be installed.
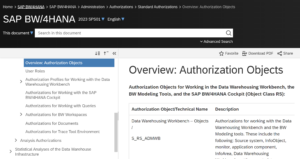
✔️ Check for Sensitive Access via Authorization Objects that are unique to BW/4HANA
Authorization Objects that are unique to BW are mostly grouped into a naming convention that starts with “S_RS_”
Your SAP Cybersecurity Solution must be able to work with these Authorization Objects in the scanning and monitoring options. SecurityBridge supports these options for BW’s unique Authorization Objects.
Here are some key Authorization Objects that are unique to BW, sourced from SAP HELP:
Auth Obj Tech Name | Authorization Object | Description |
S_RSEC | Infrastructure of analysis authorizations | Authorization for assigning and administrating analysis authorizations |
S_RS_AUTH | Analysis authorizations in role | Authorization object for including analysis authorizations in roles |
S_RS_ADMWB | Data Warehousing Workbench – Objects | Authorizations for working with the Data Warehousing Workbench and the BW Modeling tools. |
S_RS_B4H | BW4HANA Edition – Administration | Authorizations for executing programs RS_B4HANA_CHECK_ENABLE and RS_B4HANA_WHITELIST_MAINTAIN |
S_RS_IOBJA | InfoObject | Authorizations for working with individual InfoObjects with InfoAreas and their subobjects, processing and activating master data. |
S_RS_DS | DataSource | Authorizations for working with DataStore objects and their subobjects |
S_RS_TR | Transformation rules | Authorizations for working with transformation rules and their subobjects |
S_RS_ADSO | DataStore Object (Advanced) | Authorizations for working with DataStore objects (advanced) and their subobjects |
✔️ Monitor when Critical Transaction Codes are executed in BW/4HANA
When you choose the SecurityBridge Platform as your Threat Detection solution, you will be able to detect the execution of critical transactions and programs. For example, in SecurityBridge, you have the ability to include BW-specific Transaction Codes: RSU01, RSECADMIN, RSECAUTH, and RSECPROT in your list of critical transactions. These BW-specific transaction codes are sensitive because they enable the tailored administration of authorization for your BW reporting technical objects such as InfoObjects and InfoProviders.
Concluding Thoughts
Do not neglect BW/4HANA systems in your SAP Cybersecurity Scoping and Planning discussions.
BW/4HANA contains sensitive company data, sourced directly from S/4HANA.
BW/4HANA will be around for a long time to come.
Include a Solution Architect from SecurityBridge to help you on this important mission!
BW/4HANA still needs efficient management of the SAP Security Notes monthly cycle of updates. The solution architecture should include SecurityBridge Patch Management
BW/4HANA has unique technical objects not found in other SAP environments. The solution architecture should include SecurityBridge Vulnerability Management and Threat Detection Capabilities.
References:
- BW key authorization objects to review
Overview: Authorization Objects | SAP Help Portal
- Statement of Direction: SAP’s Overall Data Warehousing Strategy:
SAP Business Warehouse, SAP BW/4HANA, SAP Datasphere
- SAP Analytics Business Intelligence Statement of Direction
Statement of Direction: SAP Analytics Cloud, SAP BusinessObjects Business Intelligence (BI) solutions, SAP Crystal Reports, SAP Analysis for Microsoft Office, and SAP Lumira Designer.
https://www.sap.com/documents/2020/03/908ee705-8a7d-0010-87a3-c30de2ffd8ff.html

- An FAQ to accompany the SAP Analytics Statement of Direction:
https://www.sap.com/documents/2020/03/908ee705-8a7d-0010-87a3-c30de2ffd8ff.html

