
6 Principles for Security-by-design for SAP

Chapters
Share Article
During the last keynote of SAP’s CTO Jürgen Müller at the DSAG Technology Days 2023, it became evident why SAP is considered an industry leader for providing the best-in-class business software solutions for enterprises today. At the same time, ensuring the security of these systems has become a top priority too. However, Security-by-Design is not only a topic for software producers, but also for SAP customers running comprehensive technology stacks as the backbone of their business.
In migrating to SAP S/4HANA, many SAP-based organizations are undertaking transformation projects designed to create intelligent, sustainable, and secure business processes. We explored six security-by-design principles that SAP customers should follow to ensure the security of their systems in this article.
What is security-by-design?
Security–by–design is a principle that emphasizes the need to build security measures into software systems from the start rather than as an afterthought.
SAP projects need to embed security conciseness to respect this principle and gain a cyber-resilient application. Thus, they should prioritize security when designing and implementing their SAP systems rather than attempting to bolt on security measures afterward. This can help to prevent security breaches and minimize the damage caused by cyberattacks.
The Security-By-Design Principles for SAP:
Build on proven technology
Building on proven technology is one of the most important security-by-design principles for SAP customers. The SAP application is a reliable technology stack to build and enhance business processes. By leveraging the SAP technology stack, businesses can benefit from SAP’s proven track record of security and reliability and the vast community support and expertise available for SAP technologies.
Customers should also adopt best practices such as implementing regular software updates and patches, monitoring for vulnerabilities, and using recommended configurations to ensure the security of their SAP systems. Additionally, SAP customers can leverage intelligent and certified add-on solutions to enhance SAP, like the SecurityBridge Platform for SAP.
Create Awareness
Creating awareness among stakeholders is a critical aspect of security-by-design because its challenge is very often underestimated. It includes educating employees, customers, and partners about the importance of security and how to maintain it. All stakeholders should understand their role in establishing the system’s security, including following security standards, and reporting suspicious activity. Furthermore, project managers need to be educated and get enough room for security considerations in any IT project. In SAP environments this may seem easier than it is. Aligning SAP applications and the SAP competence center with the rest of the IT can be difficult. It requires frequent communication and knowledge exchange to bridge this gap and create a mutual understanding of the SAP specifics.
Reduce your SAP Attack Surface
Identifying and reducing the attack surface of mission-critical enterprise applications should be a constant practice. You can accomplish this by performing regular code and configuration vulnerability scans or by eliminating SM59 and RFC destinations that are no longer in use. Besides the example, there are many other steps needed to constantly identify new attack vectors and reduce the attack surface, which exposes your enterprise to risk of an impactful cyberattack.
Manage Maintainability
Managing maintainability means ensuring the system is easy to update over time. However, complex code can be challenging to maintain and may lead to technical debt and vulnerabilities over time. SAP customers should use coding best practices and consider adopting a modular approach to make the system less complex and therefore easier to maintain. This especially includes a process that allows just-in-time security patching for SAP to avoid exploitation of known vulnerabilities.
Keep Security Simple
Attack surface area and simplicity go hand in hand. In some cases, software engineering trends advocate for complex approaches over what would be straightforward code. Developers should be mindful of double negatives and complex architectures when a smoother approach would be more efficient and effective.
Additionally, guidelines and best practices need to be brought to the point to make them usable. It is too easy for human beings to become the weakest member of the chain, especially in complex environments.
Secure your SAP interfaces
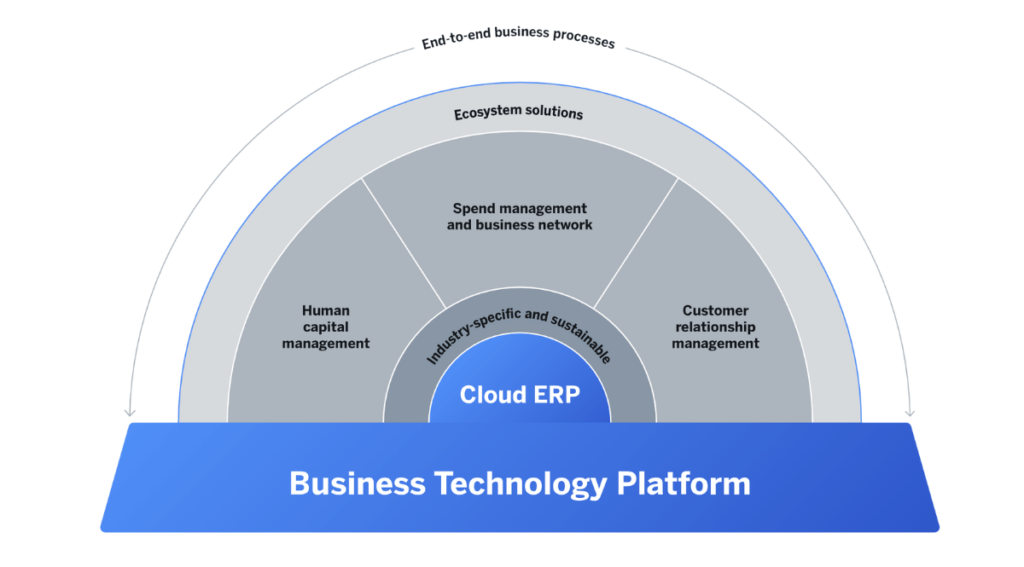
Finally, SAP customers should be concise about the data sent and received by their enterprise applications. With the growing adoption of SAP BTP caused by digitalization needs, there will be more technical communication than ever before.
It is essential to use state-of-the-art authentication methods and encrypt all data in the transfer to ensure secure data transfer. Some SAP customers already had some unpleasant surprises with expired SSL certificates because no surveillance was activated. Therefore, it is imperative to have an overview of all communication interfaces in your SAP landscape and their current state.

