SAP Information Disclosure Vulnerability

Chapters
Share Article
This article is part of our series that aims to provide SAP users with an overview of the most common vulnerability types in the SAP technology stack. While many of these vulnerabilities can also apply to other IT systems or applications, our focus is on the specific risks that SAP customers should be aware of. Organizations can take proactive measures to secure their systems and protect sensitive information from unauthorized access by understanding these vulnerabilities.
In the following sections, we will dive deeper into the specifics of information disclosure vulnerabilities in SAP systems, including how they work and how to mitigate risks. Furthermore, we will explore what are information disclosure vulnerabilities, how to exploit them, and what steps organizations can take to protect their SAP systems from these attacks.
What is an SAP Information Disclosure Vulnerability?
An SAP information disclosure vulnerability is a security flaw that enables unauthorized users to access sensitive data in SAP systems. This can include private or financial information, proprietary information, or other confidential data. Weak access controls, unpatched software, or other configuration issues that permit unauthorized access to sensitive data are just a few examples of the many causes of information disclosure vulnerabilities. These flaws can pose a serious risk to businesses that depend on SAP systems to store and manage sensitive data, so it’s crucial to regularly check and fix any potential issues to keep the system secure.
Examples of Information Disclosure Vulnerabilities in SAP:
An example of an information disclosure vulnerability in SAP can be caused by a configuration issue that allows an unauthorized user to enter the SAP system and access sensitive data stored in the system. For instance, if you don’t properly configure an SAP system, a threat actor may be able to access sensitive data without proper authorization. This could occur if you don’t set up the access control lists in the system correctly, or if there is a flaw in the software program code that allows an attacker to bypass these controls. Internet communication services residing in the PUBLIC namespace intentionally do not require authentication. Attackers know this and often acquire system information during the exploration phase.
Another example of an information disclosure vulnerability could be a flaw in an SAP application that allows an attacker to read sensitive data from the system memory or via the database management layer.
How does the exploitation of SAP information disclosure vulnerabilities work?
Attackers can exploit information disclosure vulnerabilities in diverse ways, depending on the specific weakness in the SAP system. One common method attackers use to exploit SAP information disclosure vulnerabilities is to probe the system for weaknesses. This can involve scanning the network for open ports or services, looking for default passwords or other configuration issues, or attempting to exploit known vulnerabilities in the software.
Once the attacker has identified a vulnerability that allows them to access sensitive data, they can use this information to carry out other attacks. For example, they may be able to use the stolen data to launch a spear-phishing attack or to gain access to other connected systems to the SAP system.
How to prevent information disclosure vulnerabilities?
Preventing information disclosure vulnerabilities in SAP systems requires a multi-layered approach involving a combination of technical controls, policies and procedures, and user awareness. The flaw occurs in the SAP standard product and requires precise patching, but it is also in the customer-owned program code that needs to be scanned and corrected. Additionally, an incorrect configuration can cause an information disclosure vulnerability.
How can the SecurityBridge Platform for SAP help with information disclosure vulnerabilities?
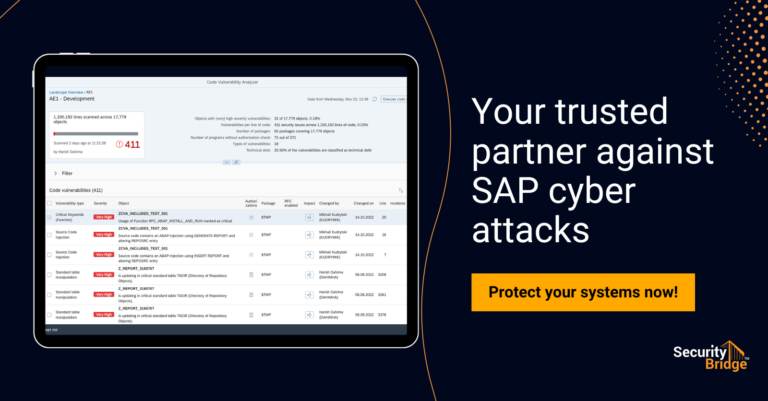
The SecurityBridge Platform for SAP is a powerful tool that can help organizations improve the security of their SAP systems and reduce the risk of information disclosure vulnerabilities. The SecurityBridge Platform provides a range of advanced cyber security features that can enhance the protection of mission-critical SAP systems.
One of the features of the SecurityBridge Platform is its vulnerability management capabilities. The solution can scan the SAP applications and database for vulnerabilities and provide detailed information on how to fix them. This helps organizations identify and address potential security weaknesses before attackers can exploit them.
The Platform also includes real-time threat detection that can surveil all SAP application log sources for suspicious activity and alert security teams in real-time to potential security incidents. This helps organizations quickly identify and respond to potential security threats before they can cause damage. It can also help organizations comply with KRITIS, GDPR, SOX, and PCI DSS regulations.
If you’re interested in learning more about the SecurityBridge Platform for SAP, we encourage you to contact us for a demo. Our team will be happy to walk you through the product’s capabilities and help you understand how it can enhance the security of your SAP systems.
Conclusion
In conclusion, the Information Disclosure Vulnerabilities in SAP systems allow unauthorized access to potentially sensitive data and can be the starting point of other types of malicious activity. There is no single activity that protects against this SAP vulnerability type.
You can reduce the risk of information disclosure vulnerabilities by implementing a comprehensive cybersecurity strategy for SAP that combines secure configuration, regular patching, monitoring for suspicious activity, conducting regular security assessments, and training and awareness programs for users. A holistic approach to SAP security can help organizations protect their systems and critical data from unauthorized access.