NIST CSF 2.0: A Winning Framework for Vulnerability Management

Chapters
Share Article
Let's Talk SAP Security
Have questions about SAP Security? We’re here to help. Contact Us
Let’s be brutally honest: No one really cares about Vulnerability Management… Until a vulnerability exploit impacts someone. We are always personally affected when an exploit negatively influences our finances, privacy, jobs, careers, or even the size of our future paychecks.
Do you agree? You know you do! This is part of our DNA – It is called “self-preservation”.
Regarding Vulnerability Management process, how do we rise above our ‘Base Self’ and work together for the greater good of our families, communities, companies, and countries by reducing cyber risk?
By reading this far, I hope you agree that Vulnerability Management is a serious topic—and for businesses, it needs to be a defined budget item. Now, let’s tie this subject matter to the SAP systems that facilitate most of the supply chain and transactions in global economies. When we combine these pivotal factors, we get “SAP Security.”
So, NOW WHAT?
Agreed. We cannot just highlight a problem without presenting a way to solve it. Managing vulnerabilities is crucial to addressing various elements of cyber risk, including minimizing the attack surface.
Understanding Vulnerability Management
Vulnerability management is a cornerstone of any robust cybersecurity strategy. It involves a continuous cycle of identifying, assessing, prioritizing, and remediating vulnerabilities across an organization’s systems, networks, and applications.
This proactive approach is essential for avoiding emerging threats and ensuring your cybersecurity posture remains strong. By effectively managing security vulnerabilities, organizations can significantly reduce the impact of cyber threats, safeguard sensitive data, and maintain operational integrity.
Remember, vulnerability scans is not a one-time task but an ongoing process that requires vigilance and adaptability based on threat intelligence.
Introduction to NIST Cybersecurity Framework (CSF)
The Cybersecurity Framework (CSF) is a NIST framework in cybersecurity, offering a structured methodology to manage and mitigate cyber risks.
Comprising five core functions – Identify, Protect, Detect, Respond, and Recover – the CSF provides a comprehensive approach to enhancing an organization’s security posture. Its flexibility and adaptability make it suitable for various industries, allowing organizations to tailor the NIST framework to their needs. Organizations can systematically address cybersecurity challenges and improve their resilience against cyber threats by adopting the NIST CSF.
What are the everyday struggles in vulnerability management?
First, let’s define a couple of challenges. Then, we will lay out a framework for successfully managing the vulnerabilities in your SAP environment. Do these affirmations sound familiar to you?
We have no idea where to start.
We cannot cope with SAP’s pace of change. We barely keep up with the threat intelligence and critical vulnerabilities that SAP announces monthly.
We need some form of automation for vulnerability scanning and management. We can’t dedicate a team member full-time to performing all that needs to be completed manually.
The security team needs a “Concept of Operations” (aka ConOps) to work on Vulnerability Management tasks.
These are all valid struggles and can be addressed through a framework that works for SAP Vulnerability Management. Identifying and addressing security gaps is crucial, and I recommend starting with the Cybersecurity Framework (CSF) from the USA National Institute of Standards (NIST).
Building a Vulnerability Management Program
Creating a robust vulnerability management program involves several critical steps. Start by identifying your organization’s critical assets and systems that need protection. Conduct regular vulnerability scans and assessments to uncover potential weaknesses.
Once the vulnerability scanning is done, prioritize these vulnerabilities based on their risk level and potential impact. Remediation should be swift and thorough, addressing the most critical vulnerabilities first. Continuous monitoring is essential to adapt to new threats and ensure your vulnerability management evolves. This structured approach mitigates risks and fortifies your organization’s security posture.
NIST Cybersecurity Framework 2.0: The Six Phases
The NIST CSF works through five phases of a cycle: Identify –> Protect –> Detect –> Respond –> Recover. The Recover phase is crucial for renewing and maintaining resilience plans after a cybersecurity incident. Now with NIST CSF 2.0, we bring that cycle back to the core of Govern.
And yes, you need some tools that are already tuned to perform these steps: Let’s break it down for Vulnerability Management:
1. Identify security gaps
Think of “Identify” in two levels:
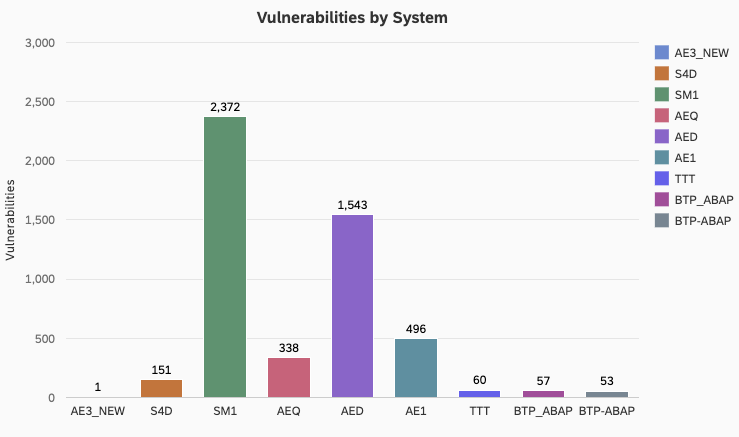
First, identify each of your SAP environments that are “in scope” for Vulnerability Management
Then, perform an automated Vulnerability Assessment (Scan) on each of these in-scope SAP environments. This will identify the specific vulnerabilities in each system. Vulnerability management data, including statistics from the National Vulnerability Database (NVD), highlights the necessity for a structured approach to effectively managing and mitigating security risks, including a robust vulnerability management plan within an organization.
2. Protect your infrastructure
I recommend protecting on 2 fronts:
First, FIX the FINDINGS! If you run a report and it comes back with a list of things that need to get fixed, the only sensible thing to do is set up a Remediation Team. This team will prioritize and triage the findings and get to work. This team needs upper management’s permission to get priority over other ongoing projects so that they “get stuff fixed.” Otherwise, the Vulnerability Scanning becomes a sad TRAGEDY where the same report gets run each week and nothing is ever improved.
Second, threat detection is a layered technique that protects your SAP environments by implementing security controls. How does this work? Think of Threat Detection as a “Mitigating Control.” It’s different from remediating vulnerabilities. However, in the case of a vulnerability that is not remediated, Threat Detection protects that vulnerable area of your environment by monitoring it for any exploitation activity. This approach assesses the effectiveness of security controls within your defense mechanisms, ensuring continuous evaluation and improvement.
3. Detect new vulnerabilities and exploitations
Both in the Vulnerability Scanning and in the Exploit Monitoring:
Detect changes in the trending results of your scheduled scans. The ideal trend is to see a regular reduction in the number and overall criticality of the findings. Trending is also impacted by NEW findings. This is commonly associated with the SAP Security Patch Day announcements each month. So, to summarize, watching the trendline of vulnerability scanning findings is a form of detection against new findings and monitoring that the number of previous exploitable vulnerabilities continues to drop over time.
In SAP Cybersecurity, the detective part of CSF is typically relegated to SAP Threat Detection. In technology environments such as ABAP, Java, and HANA databases, the technique of detecting threats is accomplished by constantly monitoring the Logs and other essential data sources. This mission is beyond what could reasonably be assigned to a human because the volume of information that must be processed from the logs is overwhelming and constantly high.
4. Respond to incidents
Through Vulnerability Remediation and Integration to SIEM partners:
Respond by having an active and involved Triage Team that will accept your Vulnerability Scan reports, prioritize the list of findings, and harmonize the remediation work with the ongoing SAP/IT projects that are also in flight. Over time, this team must diligently work the list down until all critical findings are remediated.
Respond by integrating your Threat Detection Events into a Security Information and Event Monitor (SIEM) solution and ensuring your security systems can identify vulnerabilities and gaps. Out of the SIEM, you can have Response Playbooks that dictate the method and the individuals responsible for addressing different event profiles.
5. Recover quickly
Spans across your Risk Posture, Cyber Insurance, and Backup/Archive Strategies:
Restore your company’s Risk Posture to a healthy posture. Realize that Vulnerability Findings give you a “risk health score.” To improve that score, do the obvious thing: remediate the findings.
Find out if your company utilizes Cyber Insurance. This is a relatively new category of insurance. This Area of Responsibility will typically fall to your company’s Chief Risk Officer.
Your company’s Chief Data Officer should have policies, processes, and procedures in place to act on to make sure that your environments have active backup and restore processes and procedures to ensure data security. Some of the recent cybersecurity attacks and exploits can certainly be considered disasters. So, be sure that you have plans in place to handle Disaster Recovery.
6. Govern risk
Operate from within a Risk Management team and utilize a vendor-provided best-of-breed solution for continous monitoring:
Set up a Risk Management team within your SAP and IT org structure. This team can be primarily responsible for Scanning, Monitoring, and Reporting tasks. It might also interact with a vendor of choice, such as SecurityBridge.
Operate a vendor solution so that your team can leverage Automation and Best Practices. Utilize a solution that has passed the test of time and is already providing documented value to other SAP Customers. Of course, the solution I recommend is built IN SAP, FOR SAP, and BY SAP Experts… the SecurityBridge Platform.
Do you want to discuss setting up the SecurityBridge Platform as the primary Governance solution for Cybersecurity in your SAP environments? Follow us or just reach out—I am easy to find on LinkedIn.
Measuring Vulnerability Management Success
Tracking key performance indicators (KPIs) and metrics is crucial for gauging the effectiveness of your vulnerability management plan.
Continous monitoring of vulnerabilities that has been identified and remediated, and remember pay close attention to the time-to-remediate. Metrics such as the mean time to detect (MTTD) and the mean time to respond (MTTR) provide valuable insights into your program’s efficiency.
By regularly reviewing these KPIs and metrics, organizations can identify areas for improvement and ensure that their vulnerability management efforts are yielding the desired results. This continuous evaluation is vital to maintaining a resilient security posture.
Conclusion: Why NIST CSF lays the foundation for proactive security
In conclusion, vulnerability management is an indispensable element of cybersecurity that demands continuous attention and improvement. The NIST Cybersecurity Framework offers a structured approach to managing cyber risks, and building an effective vulnerability management program involves several key steps.
By measuring the success of your program through relevant KPIs and metrics, you can ensure its effectiveness and make necessary adjustments.
Prioritizing vulnerability management reduces the risk of cyber attacks, protects sensitive information, and strengthens your organization’s security posture.
Embrace this proactive approach to safeguard your digital assets and maintain operational resilience.