Understanding the CVE-2022-22536 Vulnerability for SAP

Chapters
Share Article
SAP system vulnerabilities are most critical when they are impacting vital components which are exposed to the public internet. Such a component is the SAP Internet Communication Manager (ICM). In our article “Securing your SAP internet communication manager (ICM)” we talked about the importance of securing SAP ICM and how it works.
Today we want to dive into one particular vulnerability which every SAP administrator needs to fix immediately by applying the appropriate patch. The CVE-2022-22536 is a critical vulnerability that has the potential to put your business-critical data at risk. In this article, you learn how to mitigate it, and how SecurityBridge can help you to protect your systems from these vulnerabilities.
What is the CVE-2022-22536 vulnerability?
The CVE-2022-22536 is a critical vulnerability that affects SAP systems by targeting the SAP NetWeaver AS ABAP server. This vulnerability exploits and exposes organizations to unauthorized access, data loss and compliance. Through this vulnerability, an attacker can attach arbitrary data to any request without authentication. This results in an attacker being able to impersonate the victim and execute functions like poisoning intermediary caches.
How to mitigate the CVE-2022-22536 vulnerability?
To mitigate this vulnerability, there are a couple of essential steps that need to be considered to avoid risks. The first step to take to mitigate this vulnerability would be to apply the released SAP Security Notes (“3123396 – [CVE-2022-22536] Request smuggling and request concatenation in SAP NetWeaver, SAP Content Server, and SAP Web Dispatcher”) to close any potential entry point for attackers and harden your system’s security. Afterward, we recommend implementing an SAP System Log Monitoring. By implementing a robust logging and monitoring system you can detect earlier the malicious activities preceding the CVE-2022-22536 vulnerability. For long-term general system hardening, regular vulnerability assessments help identify vulnerabilities or misconfigured systems before any exploitation occurs from attackers.
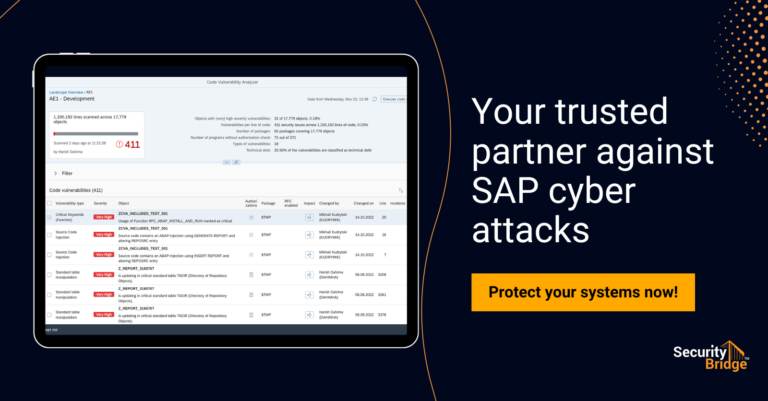
The SecurityBridge helps SAP customers implement these recommendations leveraging one common SAP security platform:
- With our Threat Detection solution, you will continuously monitor your systems and you are able to detect in real-time all potential threats and breaches to your SAP systems.
- Mitigating your vulnerabilities with our Vulnerability Management solution helps you effectively identify vulnerabilities and apply efficient remediation actions.
- Leveraging the Patch Management solution allows you to be continuously on top of the patches that must be installed in your SAP system. On the monthly SAP Patch Day, you will receive the relevant patches just in time.
- Our Security and Compliance solutions enable you in meeting regulatory requirements and hardening your SAP landscape in the long term. By providing comprehensive reports your annual security audits will run smoothly.
Conclusion
Although the CVE-2022-22536 vulnerability is a risky and complex one, by applying SAP security patches, you can constantly monitor your system. By implementing security solutions like SecurityBridge, you can mitigate in general the security risks for your SAP systems and protect them from zero-day vulnerabilities like the CVE-2022-22536. Learn more about how we can help you to protect your systems from vulnerabilities and attackers and contact us today here!