
Are you getting started with TLS 1.3 for SAP?
This new article delves into support for TLS1 3 on SAP technology stacks and presents guidelines for implementation

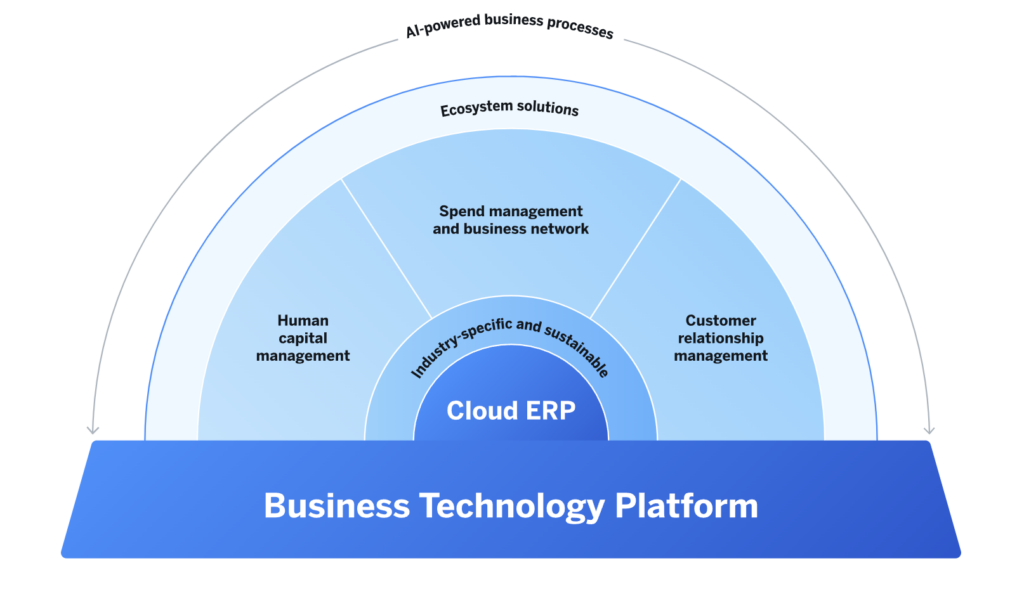
SAP Business Technology Platform (SAP BTP) is a cloud-based platform offered by SAP that provides a range of services and tools for building, extending, and integrating applications in the cloud. SAP BTP Security refers to the set of measures and practices implemented to protect the data, applications, and infrastructure within the SAP BTP environment.
Ensuring security within SAP BTP is critical to protecting sensitive business information and maintaining the integrity of applications and services. The realm of security and compliance demands a comprehensive reevaluation. New organizational processes and responsibilities must be meticulously crafted, implemented, and monitored to prevent potential chaos.
In addition to the key security aspects and the coverage by the SecurityBridge Platform discussed later in this article, organizations that adopt SAP BTP must also diligently address the following critical tasks. These include defining a staging concept, establishing development guidelines, and taking measures to prevent the creation of uncontrolled BTP subaccounts that might compromise the established staging concepts.
While SAP BTP is a new field, we can already highlight some aspects of your security considerations that are vital for every organization that plans to adopt the SAP Business Technology Platform for productive use cases.
To support the above security aspects, SAP provides the following security features to protect the BTP applications – encryption, default identity provider for enabling Single sign-on and authentication, audit logging, credential store, malware scanning, etc.
It’s possible to connect the SecurityBridge Platform with SAP BTP to enhance the security of your cloud-based SAP solutions. Here’s how the SecurityBridge Platform can work in conjunction with SAP BTP:
– If you have SAP applications or services running on SAP BTP, you can use SecurityBridge to conduct vulnerability scanning and assessments on these cloud-based SAP instances.
– This allows you to identify and address security weaknesses such as too many admin users, excessive rights granted to external users, invalid users, and configuration issues.
– SecurityBridge provides continuous monitoring for on-premises and cloud-based SAP systems, including SAP BTP applications.
– This ensures you have visibility into security events such as admin rights assignment to users in real-time.
– The SecurityBridge platform can be integrated with SAP BTP subaccounts and global accounts.
– Integration involves leveraging APIs, command line interfaces, and connectors to collect security data from cloud-based SAP instances and feed it into the SecurityBridge platform for analysis.
– SecurityBridge Threat Detection can generate real-time alerts and notifications for security incidents and vulnerabilities detected in SAP BTP environments.
– These alerts are to be sent to security teams for immediate response.
– In the event of a security incident or vulnerability discovery, SecurityBridge can provide guidance on incident response and remediation steps specific to SAP BTP environments.
– The SecurityBridge platform can assist in ensuring that your cloud-based SAP solutions on SAP BTP comply with security and regulatory requirements.
– It can generate compliance reports and evidence to demonstrate adherence to security standards.
– The SecurityBridge platform can integrate with threat intelligence sources to provide up-to-date information on threats and vulnerabilities that may impact SAP BTP deployments.
In conclusion, the SecurityBridge platform helps organizations proactively identify and respond to security threats and vulnerabilities in their SAP landscapes, ensuring the integrity and availability of critical SAP systems and data. It is a comprehensive solution for SAP security that combines scanning, monitoring, and incident response into a single platform.
Posted by
Find recent Security Advisories for SAP©
Looking into securing your SAP landscape? This white-paper tells you the “Top Mistakes to Avoid in SAP Security“. Download it now.

This new article delves into support for TLS1 3 on SAP technology stacks and presents guidelines for implementation

Download the White Paper AI 038 SAP Security Benefits Risks and Prerequisites to discover how integrating AI into SAP can enhance cybersecurity while also understanding

Learn essential SAP security practices to protect your systems and data Discover what SAP security is and how to stay compliant with industry standards <
