
Join our 4th #CrossTheBridge Cycling Event!
We are thrilled to invite you to our third annual #CrossTheBridge Cycling Event that will take place on Tuesday, June 18.
Cybersecurity and application security is a trend-driven field. While attackers continue to improve their attack techniques, defenders need to pay attention to these new trends. Follow our trending tags for information on specific topics.

We are thrilled to invite you to our third annual #CrossTheBridge Cycling Event that will take place on Tuesday, June 18.

On September 8th, 2023, we hosted the 3rd edition of our #CrossTheBridge Cycling Event. This annual gathering brought together our valued partners and customers, for a day packed with adventure, celebration, networking and, importantly, the sharing of SAP cybersecurity knowledge and insights.

From July 17th to 21st, 2023, our SecurityBridge global team gathered at our central office in Bavaria for an unforgettable All-Employee Meetup. Read on to discover the recap of that thrilling week!
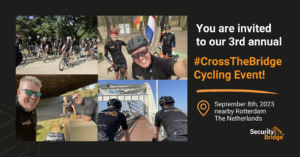
We are thrilled to invite you to our third annual #CrossTheBridge Cycling Event that will take place on Friday, September 8th.

Join our cycling community on September 9th in Brabant (NL), get a SecurityBridge cycling shirt and enjoy a wonderful day.

On September 3, 2021 SecurityBridge celebrated the successful premiere of the cross the bridge cycling event in the Netherlands. Together with customers and partners we were cycling for SAP security, a good cause, and for fun.

Applying security updates is a very effective protection against successful cyberattacks. Continue reading to learn more about security patch deployment.

Join our cycling community on September 3rd in Arnheim (NL), get one of our cycling jerseys, and support the Maartens Foundation.

Ingolstadt 28th June 2021. SecurityBridge has announced a strategic partnership with regional value-added reseller PASàPAS, located in France.

January 2021, SecurityBridge, and SAP IT security specialist, AGENTIL Group announced a partnership, to provide an integrated SAP Security Platform and services.

Ingolstadt, Germany: December 2020, ABEX, today announced to rebrand into SecurityBridge.

We are delighted to announce the addition to our team of Jaap van der Meer as Director of Sales, based in The Netherlands.
